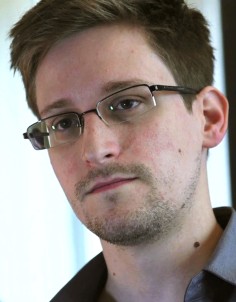
The US government is stealing millions of text messages in their hacking attacks on major Chinese mobile phone companies, Edward Snowden has told the Post
The US government is hacking Chinese mobile phone companies to steal millions of text messages, Edward Snowden has told the South China Morning Post. And the former National Security Agency contractor claims he has the evidence to prove it.
The former CIA technician and NSA contractor, hiding in Hong Kong after the US sought his arrest, made the claims after revealing to the Post that the NSA had snooped on targets in Hong Kong and on the mainland.
“There’s far more than this,” Snowden said in an interview on June 12. “The NSA does all kinds of things like hack Chinese cell phone companies to steal all of your SMS data.”
Text messaging is the most preferred communication tool in mainland China, used widely by ordinary people and government officials from formal work exchanges to small chats.
Government data show that the Chinese exchanged almost 900 billion text messages in 2012, up 2.1 per cent from the year before. China Mobile is the world’s largest mobile network carrier, with 735 million subscribers by the end of May. China Unicom, the second largest, has 258 million users. China Telecom comes in third with 172 million users.
Snowden’s leaks have rocked the international community for the past two weeks and fired up a debate about US government surveillance of citizens’ phone calls and internet browsing data without due cause.
For years, cybersecurity experts on the mainland have been concerned that telecommunications equipment was vulnerable to so-called “backdoor” attacks, taking advantage of foreign-made components. They have kept quiet because domestic hardware suppliers were still striving to catch up with their international competitors.
“China should set up a national information security review commission as soon as possible,” he said.
Telecom companies have started replacing foreign-made equipment.
China Unicom quietly replaced all Cisco routers at a key backbone hub in Wuxi, Jiangsu last year, according to the National Business Daily.
The changes are being kept quiet to avoid panic and embarrassment to the government, people in the industry say.
A series of reports based on documents provided by Snowden to The Guardian revealed how the US compelled telecommunications provider Verizon to hand over information about phone calls made by US citizens.
The leaked documents also revealed the Prism programme, which gave the US far-reaching access to internet browsing data from Google, Facebook, Apple, Skype, Yahoo and others.
The US and UK also had technology which gave them unauthorised access to Blackberry phones of delegates at two G20 summits in London in 2009, Snowden said.
The US government has defended its electronic surveillance programmes during congressional hearings with claims that up to 50 would-be terrorist attacks were foiled because of the intelligence gathered by the NSA.
US President Barack Obama says the NSA is not listening in on phone calls or reading emails unless legal requirements have been satisfied.
This article appeared in the South China Morning Post print edition as US hacked Chinese telecoms firms
----------------------------------------
来看看美国NSA头头Gen. Keith Alexander是怎么回应窃取中国手机用户短信的:(其实就一句话:我们美国需要这些信息,而且我们是在美国法律范围内行事的。)
| Gen. Keith Alexander, director of the National Security Administration, testifies on Capitol Hill in Washington, June 12, 2013, in this file photo. (Charles Dharapak/AP Photo) |
STEPHANOPOULOS: In the statement that Hong Kong put out this morning, explaining why they allowed Snowden to leave, they also say they've written to the United States government requesting clarification on the reports, based on Snowden's information, that the United States government attacked (ph) computer systems in Hong Kong.
He said that the NSA does all kinds of things like hack Chinese cell phone companies to steal all of your SMS data.
Is that true?
ALEXANDER: Well, we have interest in those who collect on us as an intelligence agency. But to say that we're willfully just collecting all sorts of data would give you the impression that we're just trying to canvas the whole world.
The fact is what we're trying to do is get the information our nation needs, the foreign intelligence, that primary mission, in this case and the case that Snowden has brought up is in defending this nation from a terrorist attack.
Now we have other intelligence interests just like other nations do. That's what you'd expect us to do. We do that right. Our main interest: who's collecting on us? And I'd just say let's look back at where that source comes from.
STEPHANOPOULOS: Well, that was the government of Hong Kong putting out that statement.
Are you confident that we have not broken the laws of Hong Kong?
ALEXANDER: I'm confident that we're following the laws that our country has in doing what we do. We have a set of laws that guide how NSA acts; we follow those laws. We have tremendous oversight by all three portions of the government: the courts, Congress and the administration.
Now when you look at these laws and the way they've been passed and the oversight mechanisms that we have, I am confident that we are following our laws.
----------------------------------------------------------
看看中国政府怎么回应斯诺登事件:(一句话:“中美两国构建新型大国关系,是前无古人、后启来者的伟大事业。”)
得益于长期以来的积累,中美合作具有很好的基础。但是,某些美国政客操纵的暗流并没有退去,仍在借机对中美关系的主流进行冲击。这股暗流干扰美国对华政策的连贯性,阻碍中美两国建立战略互信。中美关系大船沿着既定航线稳定前行,就必须提防和遏制这股暗流的干扰。
回顾中美重新打开交往大门40多年的历史,两国经历的一些风雨完全是某些美国政客一手制造出来的。在“棱镜门”和中国之间建立“新关联”,无异于在中美关系的晴空布下一块新的阴云。阴云不除,贻害无穷。道理很简单,阴云不仅遮蔽阳光,集聚到一处,还真有可能掉下几滴雨点来。用好“新关联”这部反面教材,就是不能让“新关联”不了了之。胡言乱语不付出必要的代价,某些人继续扮演“大嘴”的冲动就难以消除。
中美两国构建新型大国关系,是前无古人、后启来者的伟大事业。双方既要大处着眼、登高望远,又要小处着手、积微成著。不断积累正能量,为中美关系营造良好氛围,至关重要。